Genetec urges privacy-by-design approach as physical security data volumes surge
As surveillance systems generate ever-growing volumes of sensitive data, Genetec is urging organisations to embed privacy-by-design principles and stronger governance controls into their physical security operations.
As organisations deploy more cameras, access control systems and automated license plate recognition tools, the data generated by physical security infrastructure is becoming both an operational asset and a growing concern.
Genetec Inc., a global provider of enterprise physical security software, has outlined a set of best practices aimed at helping organisations safeguard sensitive data without undermining the effectiveness of their security operations.
The company argues that physical security systems now produce vast streams of video footage, access logs and vehicle data that increasingly feed into investigations, compliance reporting and operational decision-making. But as reliance on this data grows, so too does regulatory scrutiny and exposure to cyber threats.
Mathieu Chevalier, principal security architect at Genetec, cautions that physical security data can be highly sensitive and should not be treated as a commercial asset to be exploited beyond its original purpose.
He warns that some market approaches risk expanding the use of collected data in ways that create privacy vulnerabilities. Instead, he says, organisations should demand clear limits on how their data is used, enforce strong lifecycle controls and adopt technologies designed to respect privacy by default.
The emphasis on “privacy by design” reflects a broader shift in corporate governance, where compliance is no longer limited to IT departments but extends to facilities management, risk teams and executive leadership.
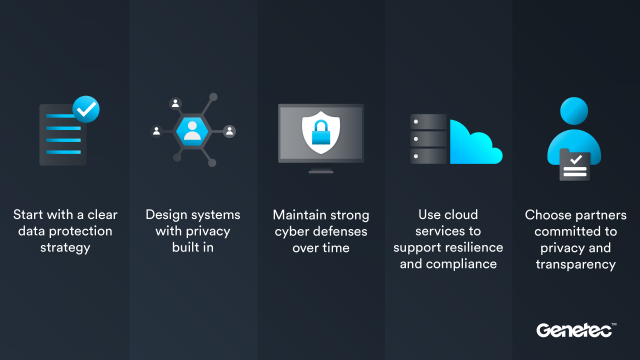
Genetec’s first recommendation is the development of a clear and documented data protection strategy. Organisations are encouraged to regularly assess what data they collect, why it is collected, where it is stored, how long it is retained and who has access to it.
Such documentation, the company argues, reduces unnecessary data exposure and helps identify policy gaps before regulators or cybercriminals do. It also enhances transparency, an increasingly critical factor in maintaining trust among employees, customers and the public.
 In many jurisdictions, evolving data protection frameworks have blurred the line between physical and digital security. Video footage and biometric identifiers, once viewed as operational tools, are now squarely within the scope of privacy regulation.
In many jurisdictions, evolving data protection frameworks have blurred the line between physical and digital security. Video footage and biometric identifiers, once viewed as operational tools, are now squarely within the scope of privacy regulation.
A second pillar of Genetec’s guidance focuses on designing systems with privacy controls integrated from the outset. This includes applying purpose limitation and data minimisation principles to ensure that only data necessary for defined security objectives is collected and retained.
The company recommends encrypting data both in transit and at rest, enforcing strong authentication protocols and implementing granular access controls. It also points to privacy-enhancing technologies such as automated anonymisation and masking to reduce identity exposure while preserving the operational utility of footage and records.
This approach reflects growing concern that surveillance technologies, particularly when combined with artificial intelligence, can expand beyond their intended scope if not tightly governed.
Treating cybersecurity as continuous
Genetec also frames data protection as an ongoing operational discipline rather than a one-time compliance exercise. Regular system hardening, vulnerability management and timely software updates are described as essential safeguards in a threat environment where attack vectors evolve rapidly.
The convergence of physical and cyber domains means that a breach of surveillance infrastructure can compromise not only privacy but also operational continuity. As more systems become networked, physical security teams increasingly find themselves operating within the broader cybersecurity ecosystem.
The company further highlights the role of cloud-managed and software-as-a-service deployments in strengthening resilience and compliance. Cloud environments can simplify patch management and ensure that privacy controls remain current, while also offering flexibility in balancing scalability and data residency requirements.
However, Genetec underscores that technology choices alone are insufficient. Organisations are urged to evaluate vendors based on transparent data governance practices, clearly defined limits on data use and independent security certifications such as ISO/IEC 27001, ISO/IEC 27017 and SOC 2 Type II attestations.
Vendor vulnerability disclosure processes and the ethical deployment of artificial intelligence—particularly where personal data is involved—are also identified as critical due diligence factors.
The recommendations signal a broader industry recognition that physical security can no longer be managed as a siloed operational function. As video management, access control and analytics platforms become more sophisticated and interconnected, they create expansive data ecosystems that demand robust oversight.
Founded in Montreal more than 25 years ago, Genetec serves over 42,500 customers across 159 countries, providing video management, access control and automatic license plate recognition solutions built on an open architecture.
Its latest guidance suggests that in the race to enhance security capabilities, organisations must give equal weight to the governance frameworks that protect the very people those systems are meant to secure.


 Why the Equity Leaders Program should become Africa’s benchmark for CSR
Why the Equity Leaders Program should become Africa’s benchmark for CSR
 COMESA dismisses viral claims of KES 7.8 Billion fine against Airtel Kenya
COMESA dismisses viral claims of KES 7.8 Billion fine against Airtel Kenya
 Qatar Airways launches Doha–Port Sudan route as it expands African network with major frequency increases
Qatar Airways launches Doha–Port Sudan route as it expands African network with major frequency increases
 Equity Group eyes AI systems to become Transformation Finance Institution
Equity Group eyes AI systems to become Transformation Finance Institution
 PayPal expands digital dollar to Africa in boost for Uganda’s cross-border trade
PayPal expands digital dollar to Africa in boost for Uganda’s cross-border trade
 Uganda exports first consignment of chilled cut meat to Saudi Arabia
Uganda exports first consignment of chilled cut meat to Saudi Arabia